Tools of the Trade: Getting Inside Cyber Security

How do students respond to your experiences and what you bring to the table?
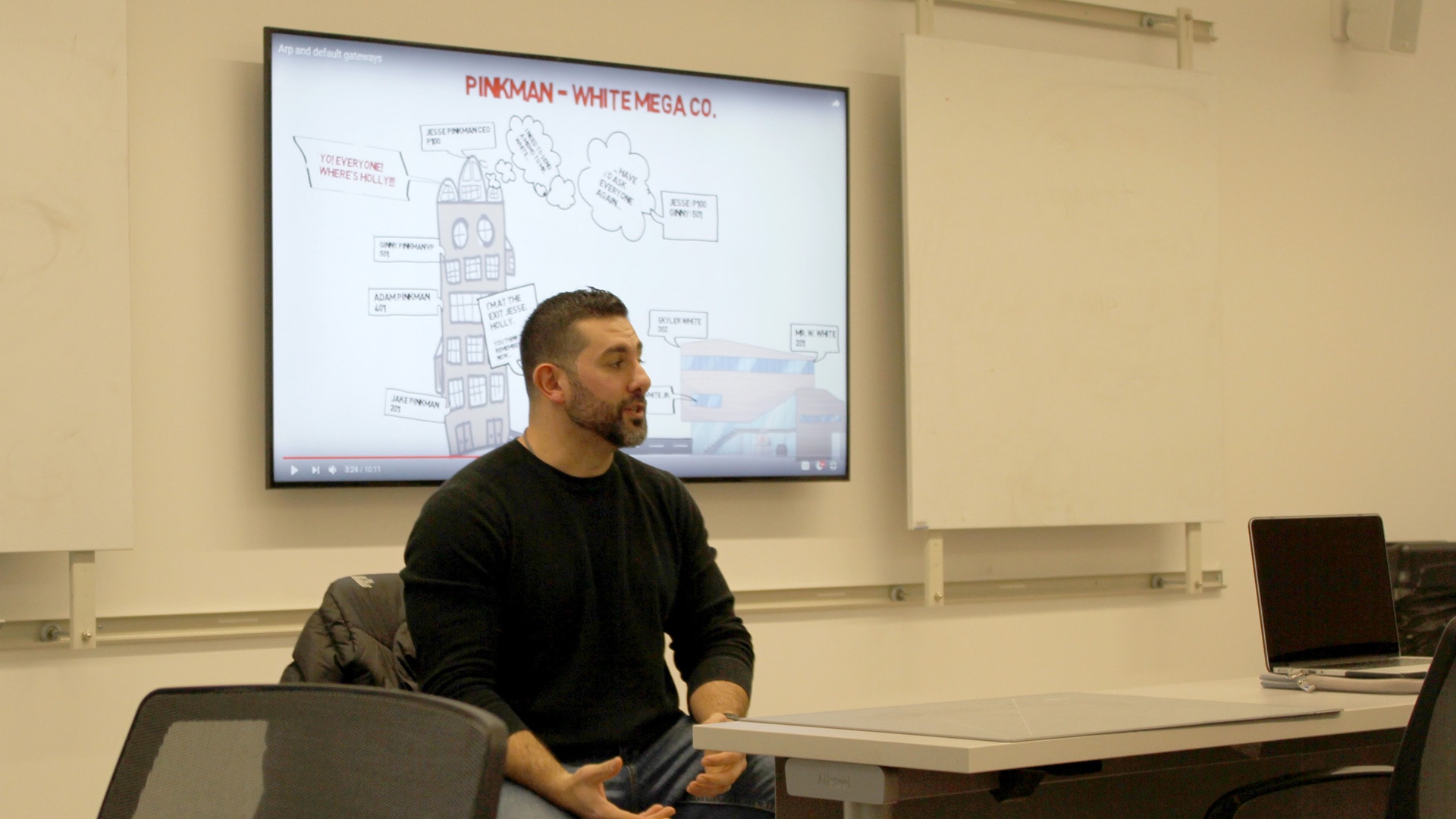
I’ve learned that teaching out of textbook is the wrong way to do things, especially in a program like this. The first week [of class] I went around the room and asked students what they thought the biggest takeaway was for them from this class. And they wanted a skill set. They didn't want to just get a piece of paper and learn out of a textbook. They wanted to do a lot of hands-on learning. So, what I try to do is for half of the week I focus on the prerequisites of the course with content out of the textbook. But the second half of the week, I start introducing new tools. When I'm introducing a new tool to the class I explain to them the ramifications of learning this new tool.What do you mean by tools?
Certain operating system tools that I’ve used daily in forensics work, cyber intelligence work, penetration testing, white-hat hacking and similar types of work that I do. I let the students know that these aren’t just random tools that I'm teaching them — they’re actually tools I use on a daily basis. I let them know that these are great tools to include on their résumés, and show them the types of jobs that revolve around each tool."There’s always that one concept or that one tool that’s going to ignite a passion in students."
What I'm trying to tell students is that in every class they take, there’s always that one concept or that one tool that’s going to ignite a passion in them. This class might be a prerequisite, but students should really focus on what they can take away from it and really use that to make a determination for future classes, or future grad school programs, or even future jobs.
It must be nice for the students to be able to identify certain operating system tools that you’ve discussed in class and relate them to a specific job.
Absolutely. At the end of the day everyone wants a job, right? I think our students are getting excited [about the future], especially when they’re carrying out hands-on labs and they're actually learning a new skill."The skills they're learning in this particular class will either get them a job in the future or land them in jail."
I'm empowering the students to either do something really good or really bad. The skills they're learning in this particular class will either get them a job in the future or land them in jail. There's a lot of responsibility that comes along with it, but that excites them even more. The fact that they're actually learning a skill that they can put on the résumé and then can look for a job even before graduation — that’s what's exciting to them.
How do you help students understand the responsibilities that come with working in this industry?
One of the first things that I do is show the students the Rhode Island State Police website because they basically detail the computer crime laws in Rhode Island. We talk about what they can do and especially what they can't do. When we get into more mature tools or more mature skill sets, I always point them back to that resource. Just because somebody has their front door unlocked, it doesn't mean you can walk into their house.
What’s an example of what a student might work on in class?
The other day we started class with about a half hour lecture right from the textbook. And then we backed it up with the introduction of a new tool. We spent time mapping out the internal network of the classroom, identifying all the connected devices to the internal network. And then each [student] carried out a comprehensive scan of somebody else's machine on the network. They were able to identify if there were any vulnerabilities that existed on somebody else's machine. Identifying the operating system, enumerating any open ports, things like that.This was the mature way, the responsible way of doing it. But I told them, they can go to Starbucks and enumerate the entire internal network and do the same thing, but that would be the wrong way to do it. I introduce a certain number of network forensic concepts that go along with an investigation, like when I used to, we'll say “eavesdrop” on behalf of the government, and let them know why I would use a specific tool, how I would use it out on the field and then what I would be looking for in terms of results from it.
"In this field, something's always happening."
How do you incorporate current events into your class? How do the students react to that?
In this field, something's always happening. Whether or not it’s talked about in the mainstream media, something is always happening. Usually, I try to introduce a real-world event on a weekly basis. To give you an example, for the Spectre and Meltdown vulnerabilities that were discovered recently, only about a quarter of the class had actually heard about it because it happened over the winter break. So, in class, we started out with about fifteen minutes for everyone to just become familiar with what happened. I asked students to spend a little time reading up about it. Then I devoted the entire class to this discussion. Usually, when something like that comes up, that takes precedence over whatever is in the textbook. Especially when it’s something like that particular vulnerability that has such a wide impact.
This is an operating system class, so I told the class “let's dive into this and see how it affects everybody in here.” Towards the end of the class we worked on a scenario where I had each student write an executive summary as if they were working at the security operations center for a large Fortune 500 company.
When I worked in a security operations center, something like this would happen once a week and I would have to do it. I got very good at writing executive summaries for CEO’s, for chief financial officers, you name it. Basically they [senior leadership] want to know what's going on, how does this impact the company, and lastly are there any work arounds in place, how do we mitigate the eventual risk — and that’s what an executive summary does. The students got really into it, and each one of them produced a one-page summary. This is a big part of this program as well: introducing students to technical writing. We focus on teaching them to capture something that's technical in nature and write it for someone that might not be technically minded.
How is JWU doing compared to other universities that are preparing students for this field?
Just the facilities available here demonstrate the commitment the university is making to the students. The university making the investments in infrastructure and innovation, that’s already setting the students up for success just by the nature of their surroundings.This industry changes every single day. There are new vulnerabilities constantly being discovered, new exploits being created, new project techniques being thought of and the university, just by the infrastructure it has, is already 80% ahead of the game.
"Innovative thinking is critical in a program like this."